Is Passwordless Authentication the Future?
Posted July 8, 2021 by Sayers

When it comes to hacks and data breaches, what is the most common way cybercriminals breach sensitive information? Are they master hackers that can bypass firewalls and other security measures? Not quite.
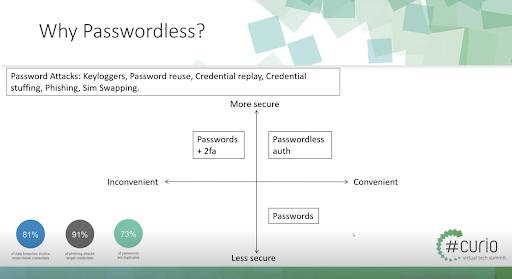
More often, breaches are simply from an actor logging into the system with stolen credentials. To support this use of identity-based breaches, phishing attacks often focus primarily on targeting credentials.
It’s no surprise why cybercriminals are after passwords. With just over seventy percent of passwords being duplicates, acquiring a single password almost guarantees access to a greater number of applications and data like a victim’s email, bank accounts, or web applications.
Many businesses have been affected by password authentication for quite some time. So, what’s the solution? Enter passwordless authentication, an emerging technology that will take hold in the next couple of years. Today we’ll be discussing the ins and outs of passwordless authentication and why it works so well to keep out external threats.
What is Passwordless Authentication?
Passwordless authentication is the removal of a password as a factor for obtaining access to a system. It then replaces the need for a password with embedded device trust features, biometrics, and user interaction. Manufacturers such as Apple have Face ID, Microsoft has Windows Hello, in addition to other hardware and software-based solutions that leverage Phone Factor and other technological advanced capabilities.
Passwordless authentication should not be confused with a password-free solution, which still uses a password but hides it from the user by a biometric lock or hiding it in the browser.
The User Experience of a Passwordless Solution
The user experience for passwordless authentication is seamless and will not add unnecessary time to the overall login process.
To illustrate this, here is how Microsoft’s Modern Authentication passwordless solution works from the user’s experience.
- Step 1: Open Microsoft app or Saas service
- Step 2: Enter email address
- Step 3: Receive a prompt with a two-digit number
- Step 4: Unlock mobile device
- Step 5: Select the corresponding two-digit number in the authenticator app
- Step 6: Confirm mobile device biometrics
While it may take a bit of getting used to, the passwordless authentication process is seamless and user-friendly.
Passwordless Authentication: A Matter of Security and Convenience
With the addition of passwordless authentication, there are now three distinct ways companies can keep their systems secure, each with varying levels of convenience and security.
First, we have the traditional password method. While extremely convenient, it is easily the least secure option of the three. Falling victim to a phishing scam can spell disaster in terms of an outside entity gaining access to a network.
Second, we saw the prevailing opinion that implementing passwords with two-factor authentication would solve this security problem. For the most part, it did the trick. Now, if someone were to steal a password through a phishing scam or similar trap, they would still need to know the security questions that accompany the login process. However, there is a loss of convenience for the user. Not only must they remember their password, but they also must remember the answers to the additional security questions.
Finally, by removing passwords altogether, passwordless authentication makes it convenient for the user by not having to remember all their various personal and business login credentials. For this reason, it is also the most secure option.
How to Go Passwordless
When it comes to using passwordless, keep it simple and leverage what solutions you have already. For example, find out if your current password vendor offers passwordless authentication. In addition, focus your efforts on your remote access points, as well as SaaS—which likely supports passwordless authentication already.
While there are currently some options for passwordless authentication on the market today, it won’t be long before they become commonly used by enterprises everywhere. By 2022, 60 percent of global enterprises and 90 percent of midsize enterprises will have implemented passwordless methods.
Work With Sayers For All Your Cybersecurity Needs
Whether you’re looking to update your cybersecurity process or want to know where your vulnerabilities in your system are, we’ll help get your security solutions implemented, optimized, and integrated quickly. Our team of experienced and talented cybersecurity experts will ensure that your solutions are secure, compliant, and in line with today’s security best practices.
When it comes to your cybersecurity, there are no shortcuts. Contact Sayers today to ensure the safety and security of your data.


