

Author: Chris Cochran
Chris is Creative Director and Cybersecurity Advocate at Axonius, co-founder of Hacker Valley Media, and producer/host of the award-winning Hacker Valley Studio Podcast. Chris has extensive experience building and running strong cybersecurity and content programs. For more on the topic of cybersecurity asset management, watch the 17-minute “Bridging the CAASM” session presented by Chris at the Sayers #Curio Virtual Tech Summit, available free on demand.
Look at any cybersecurity lifecycle framework and you’ll see the first step is likely identify – identify assets, resources, and risks. Despite that priority, many businesses struggle with having a complete, up-to-date inventory of all assets in their environment.
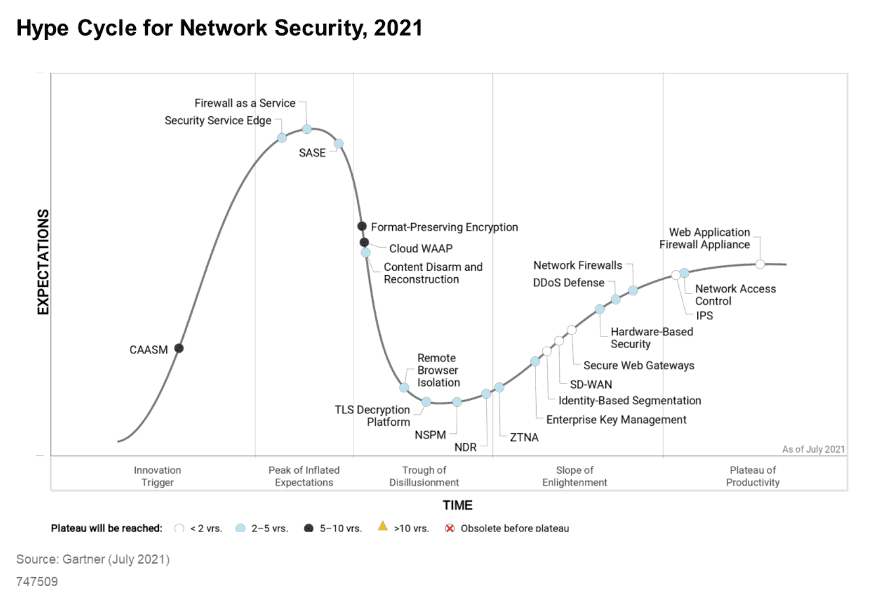
Think of assets as anything with an IP address that connects to network resources for your organization, such as servers, endpoints, and bring your own devices, as well as applications and licenses. Not to mention what’s running in the cloud and across the Internet of Things.
Source: NIST Cybersecurity Framework nist.gov/cyberframework
Organizations that get that first step right using an effective approach to asset management are better positioned to protect their environment from threats, detect and respond to cybersecurity events, and recover and restore operations and services for business continuity.
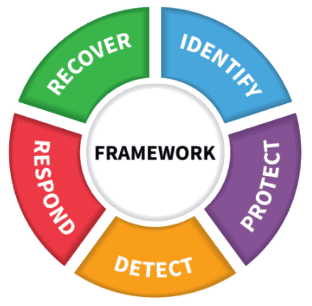
As an emerging category of solutions, CAASM allows organizations to see all assets regardless of where they reside, discover security coverage gaps and risk, and take action to enforce security policies.
Gartner coined the term in their 2021 Hype Cycle for Network Security, defining CAASM as “an emerging technology focused on enabling security teams to solve persistent asset visibility and vulnerability challenges.”
Using API integrations with existing tools in your environment, CAASM provides a consolidated view of all assets – both internal and external – then identifies cybersecurity gaps and provides automated steps to remediate issues.
“For business continuity or disaster preparedness, you need to understand all the things that can go wrong and how to prepare for them ahead of time,” says Chris Cochran, Creative Director at Axonius, an emerging CAASM vendor. “CAASM will help us get that holistic picture within our environment to understand what technologies we use, where our assets are, and how we can keep ourselves safe from some of these higher-level threats.”
Cochran adds that crossing the CAASM means getting additional context about your assets so you can discover coverage gaps and risk. Then you can take corrective action to safeguard your environment, mitigate issues, and keep operations running.
Asset management boils down to a simple concept: You can’t protect what you don’t know about. Cochran says:
“Not understanding what’s going on in your environment will be detrimental to any business continuity plan. Because if you have things you don’t even know exist, how are you going to make sure those things have a failover or any type of redundancy to keep those operations moving forward?”
From an incident response and business continuity perspective, you have to know all the devices in your environment if you’re going to find the incident’s root cause. Otherwise you risk spinning your personnel, money, and other resources because you overlooked a laptop or server that was the initial jumping point for an attacker.
Some companies use a configuration management database (CMDB) to store information about their IT environment. But CMDB tends to fall short of the context and intelligence that CAASM can provide.
“CMDB establishes some of the relationships and dependencies between assets, but it doesn’t quite give you the entire context in relation to the rest of the technological ecosystem,” Cochran says. “It is not an asset management tool.”
Without an updated, unified view of everything in your environment, your organization is left open to unknown gaps in security. A CAASM platform such as Axonius integrates with your network and solutions – more than 400 sources of business, IT, and security data – to inventory all your assets in a matter of hours.
“From a technological perspective, we are asking several different solutions about a single device, so we can get that comprehensive 360-degree view of what that asset looks like in your environment,” Cochran says.
CAASM’s holistic view then protects assets step by step:
Once you’ve used CAASM to identify all the assets in your IT environment (visibility), CAASM solutions give organizations the ability to ask questions to get context about those assets (observability).
For every asset, you want to know answers to the following:
CAASM goes beyond asset inventory to help you understand which assets are secured and managed, and which need attention. By integrating with your network infrastructure and a variety of data sources, a CAASM solution can identify a range of risks to your environment. Examples of such risks include:
CAASM solutions work to continuously surface coverage gaps before automatically initiating corrective actions.
CAASM’s policy enforcement automatically applies security policies to help protect assets against attack. The Axonius platform uses an action library with more than 80 configurable actions to automate response and remediation for devices, cloud assets, and users.
These actions range from deploying software and running remote commands, to enabling or disabling users and isolating devices from a network.
Using CAASM for cyber asset management not only helps identify and remediate security gaps, it also reduces the manual work many organizations struggle with to meet requirements for governance, risk management, and compliance (GRC).
An effective CAASM solution streamlines reporting by providing the automation to more quickly answer a GRC auditor’s questions and provide proof of compliance.
——————
Learn more about CAASM and other cybersecurity services from Sayers to fit your business needs.